In today’s threat landscape, traditional perimeter defenses are no longer enough. As cyberattacks grow more advanced—and as remote work, cloud adoption, and BYOD (bring your own device) continue to rise—organizations need a security model that goes beyond “trust but verify.” That’s where Zero Trust comes in.
What Is Zero Trust?
Zero Trust is a cybersecurity framework that assumes no user or device should be trusted by default, even if it’s inside the corporate network. Instead, access is granted based on identity, behavior, and context—validated continuously. The core principle?
“Never trust. Always verify.”
Why Growing Organizations Should Adopt Zero Trust
For mid-sized and growing companies, Zero Trust offers critical benefits:
- Limits lateral movement in case of a breach
- Protects sensitive data across on-prem and cloud environments
- Supports compliance with HIPAA, CMMC, NIST, and other frameworks
- Improves resilience without adding complexity
The good news: you don’t need to “rip and replace” your entire infrastructure. Zero Trust can be implemented in phases—and adapted to your business’s unique needs.
The Zero Trust Maturity Model
Zero Trust is not a one-time project—it’s a journey. Here’s a typical maturity path:
Stage 1: Initial (Basic)
- Flat network, minimal segmentation
- Limited visibility into users/devices
- Basic security tools (antivirus, firewalls)
- High risk of insider threats and lateral movement
Stage 2: Developing (Intermediate)
- Network segmentation and role-based access
- Conditional access policies
- MFA and endpoint detection & response (EDR)
- Improved visibility, but still maturing
Stage 3: Mature (Advanced)
- Fully segmented environments
- Automated, policy-based access control
- Real-time risk scoring and threat response
- Strong data protection and adaptive security posture
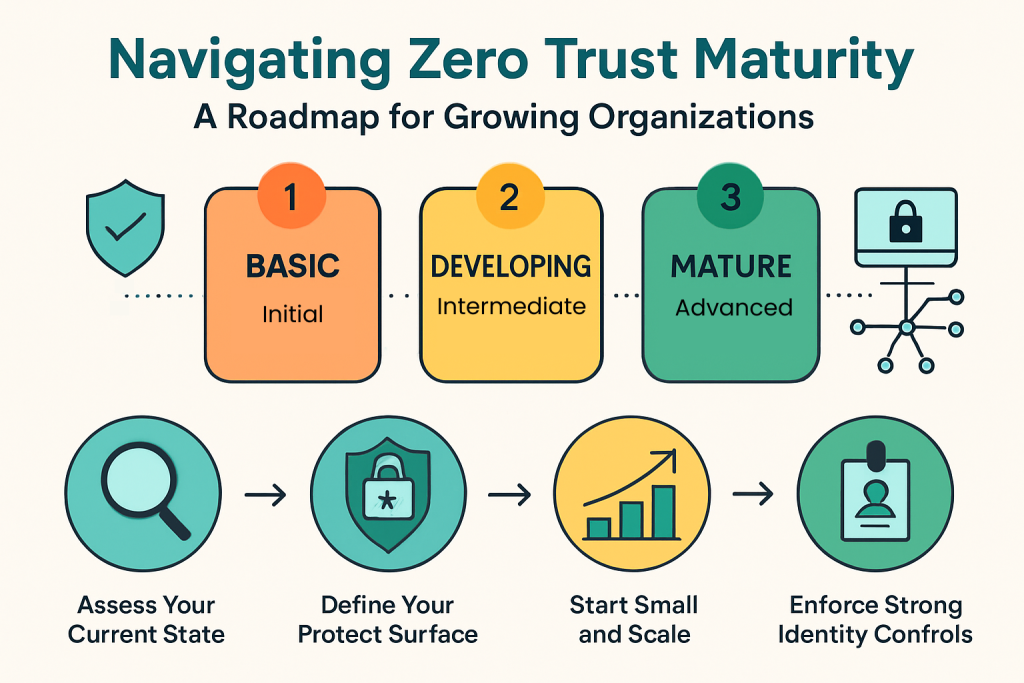
How to Build Your Zero Trust Roadmap
Here’s a step-by-step plan to help your organization transition to Zero Trust.
1. Assess Your Current State
- Map out users, devices, applications, and data
- Identify critical assets (your “crown jewels”)
- Evaluate current gaps in access controls and visibility
2. Define Your Protect Surface
Unlike a network perimeter, a protect surface includes only what truly matters, such as:
- Customer records
- Financial systems
- Core business apps (e.g., Salesforce, Office 365)
- Confidential IP or trade secrets
Focus protection efforts here first.
3. Start Small and Scale
Rather than a massive overhaul, pick one area—like HR or Finance—and:
- Apply Zero Trust policies
- Monitor behavior and outcomes
- Adjust before rolling out more broadly
4. Enforce Strong Identity Controls
Identity is central to Zero Trust. Key steps include:
- Enabling Multi-Factor Authentication (MFA)
- Using Identity and Access Management (IAM)
- Granting least privilege access based on role
- Monitoring for suspicious activity or sign-in attempts
5. Use Micro-Segmentation
Micro-segmentation divides your network into smaller, secure zones. This:
- Limits lateral movement
- Isolates critical systems
- Prevents attackers from moving freely if they gain access
Tools like software-defined perimeters and next-gen firewalls can help enforce this segmentation.
6. Automate and Monitor Continuously
Zero Trust is dynamic—not static. Use automation and AI-driven tools to:
- Continuously monitor access and behavior
- Enforce policies in real time
- Automatically adjust access based on user risk
This reduces response time and prevents small incidents from becoming major breaches.
Key Metrics to Track Progress
Measuring ROI and success is essential. Track these metrics:
- Time to detect/respond to threats
- Number of privileged access accounts (lower is better)
- Audit pass/fail rates on access controls
- Reduced lateral movement incidents
- Improved compliance scores
These indicators can help you benchmark progress and justify further investment in Zero Trust initiatives.
Common Challenges (And How to Overcome Them)
- “We’re too small for Zero Trust.” Even small businesses benefit—especially those handling sensitive data.
- “It sounds too complex.” Start small. A phased rollout focused on high-risk areas makes it manageable.
- “We don’t have the resources.” Partnering with a managed IT and security provider can fill the gaps with expert guidance and implementation support.
Zero Trust Doesn’t Mean Zero Productivity
Some fear Zero Trust will slow down users. When done right, it enhances the user experience with:
- Seamless SSO (Single Sign-On)
- Smarter access that adjusts based on risk
- Fewer security interruptions and breaches
Security and productivity don’t have to compete—they can work together.
Final Thoughts: A Future-Proof Strategy
Zero Trust isn’t just a buzzword—it’s a strategic security shift that prepares your organization for future challenges. With a structured approach, growing businesses can reduce risk, improve compliance, and build a security foundation that scales with them.
Ready to build your Zero Trust roadmap?
Kamin Associates can help assess your current environment, plan your strategy, and implement the right tools—without disrupting your operations.
👉 Contact us today to start the conversation.